all posts (default)
general
bash scripting
mac
plain text
reading
travel
windows
www
Info:
©Jim Brown
Weblog (or Blog)
Monday, May 30, 2022
Blog No Longer Updated
I'm leaving this blog posted for reference to the information it has. Some of it, especially that related to using computers, the Windows operating system, and plain text, is particularly good. Feel free to email me with any comments or questions.
posted at: 11:16 | path: /general | permanent link
Sunday, May 29, 2022
It's Been Fun
I've had a site on the web since late 1997. Much of the time that site included a blog or blog-like page, mostly about Clemson football or using a Windows computer. I've occasionally posted opinions on other topics, usually politics, but by and large, I did not do it consistently enough to develop any sort of a following.
I used to spend a lot of time developing my website, playing with different layouts and graphics. I learned how to use SSH to maintain it, which was a challenge for someone who has used Windows all his work and personal life and is self-taught on computers.
But, I don't post much anymore and I question whether it's worth the $50 dollars or so I spend every year to maintain the domain name and website. There are plenty of free alternatives for email. There is even free web hosting if I feel the need for a presence on the web, for example, https://jcb37310.github.io.
So, for now, this is goodbye. It will be a while before jcby.com goes away—I am paid up through 2023, but this will be my last post here...until it isn't.
posted at: 12:01 | path: /general | permanent link
Thursday, March 31, 2022
Global Economics After Ukraine
An interesting and comprehensive look at what the future of globalization might look like after Putin's invasion of Ukraine. To my limited knowledge, this article at least tries to look back at history and project what the ultimate meaning of Ukraine in terms of the global economy might look like.
posted at: 06:48 | path: /general | permanent link
Wednesday, February 23, 2022
Lenovo ThinkBook 13s
Two years ago I posted about a new computer I had gotten. I was excited about it because it was powered by an Intel i7 8th Generation and I had never had a Windows machine with that kind of power. I had also used ThinkPads for years and loved their construction and especially their keyboard. I said in a February 2020 post that I would write a review of the new computer. This is the review.
Why wait 2 years to write a review? Because for about 20% of that time, it's been out of service due to various problems. It's finally stable enough to use, although there are some issues, and it is an okay machine--just okay.
Pros
- Fast
- Runs Windows 11
Cons
- Began acting up almost out of the box. Biggest problem was that it would not wake from sleep. Sent to Lenovo Repair Depot. Came back 49 days (!) later with new motherboard.
- Still lots of problems. Lenovo had trouble with its Repair Depot so switched me to Onsite Service.
- Three months, 2 more motherboards, and 2 new trackpads later, computer seems to run okay.
- However, trackpad is too sensitive even on lowest sensitivity setting. Cursor jumps when typing. Hovering finger even a half inch above trackpad initiates a tap.
- Two keys are sticking frequently and one won't engage its base and sticks up above other keys, even though it's still hanging on there (i.e., it has not come completely loose).
So after all the maintenance its an okay machine but hard to use because of the keyboard and trackpad issues. I would not recommend this machine or any of its successors that share the same body and keyboard (my version has been discontinued after only two years in production).
posted at: 08:10 | path: /general | permanent link
Wednesday, December 22, 2021
What is Wrong with Republicans?
Trump got booed by his supporters when he acknowledged he got the booster vaccine. What is wrong with these people? Why do they think this thing that's good for their health (and everyone's) is a political issue? I used to be a Republican. Now I think they have lost their minds--and any integrity they may have had.
posted at: 10:38 | path: /general | permanent link
Wednesday, September 22, 2021
So Wrong!
The Charleston Post and Courier has an opinion column today saying that SC should spend money to entice people to get the COVID-19 vaccine. That is so wrong. Why should you pay people who make a stupid decision not to get vaccinated? SC should pass a law requiring vaccines.
posted at: 07:33 | path: /general | permanent link
Friday, September 17, 2021
9/11
If you only read one article about the 20th anniversary of September 11, 2001, read this one.
posted at: 17:57 | path: /general | permanent link
Sunday, August 08, 2021
Can You Change Your Mind?
David French, a senior editor of The Dispatch, a columnist at Time, and the author of “Divided We Fall,” reviewed Andrew Sullivan's book, "Out on a Limb" in today's New York Times. His review causes me to want to read the book.
But French said something in his review that struck a chord with me:
"This world is almost impossibly complex. Conventional wisdom is frequently wrong. No partisan side has a monopoly on truth. In these circumstances, a nation needs writers and thinkers who will say hard things, whose fearlessness gives you confidence that you’re hearing their true thoughts."
posted at: 12:26 | path: /general | permanent link
Friday, June 04, 2021
Land of the Free???
Peggy Noonan tries to explain why the world is going crazy.
posted at: 11:27 | path: /general | permanent link
Friday, March 19, 2021
Getting to be Travel Time Again!
If you click on the travel item in the list of Filter Blog Posts By:, you will see that the last post is November 2019, after our cruise to Alaska. Winter weather and then COVID-19 stopped travel after that. But the end of our lockdown is near! Debbie and I have our COVID-19 vaccines. (I hope you have yours as the only way we will defeat COVID-19 is to vaccinate about 75% of the world's population.) The number of cases is dropping, the weather is getting warmer, and we are starting to think about our first trip in over 18 months. Hallelujah!!
posted at: 10:05 | path: /travel | permanent link
Tuesday, February 23, 2021
Fun Reading for Geeks
Like most folks that got into computers early, I played quite a few games over the years. Games were never my primary interest (information management was). But I can remember spending hours after work playing on the company's computers the simple text games or graphical games (very few of those) in the early 1970s. One I especially remember was Lunar Lander. I just stumbled across a new website called 50 Years of Text Games that is just plain fun reading for those that played those early games. Recommended.
posted at: 09:49 | path: /reading | permanent link
Thursday, January 21, 2021
Who Is Guy P. Harrison?
My post "Why QAnon Can Exist" cites an essay I found riveting and eminently relevant for today's world. It caused me to wonder who is Guy Harrison and what else has he written? Several excellent essays are linked there. Enjoy.
posted at: 16:25 | path: /general | permanent link
Why QAnon Can Exist
Wow, what an essay here! Read it, study it, act on it!
posted at: 16:12 | path: /general | permanent link
Friday, January 08, 2021
Insurrection and Sedition
It is still hard to believe that the President of the United States, who took an oath to defend the Constitution, incited a mob to attack our Capitol. As usual, Peggy Noonan expresses my thoughts better than I could.
posted at: 08:34 | path: /general | permanent link
Sunday, November 29, 2020
Plain Text Life
I've linked to several articles about how others use plain text. Mark Koester's post is one of the most complete I have ever read. Recommended.
posted at: 10:46 | path: /plain_text | permanent link
Tuesday, November 24, 2020
Remember This Next Year
If the economy turns toward recession next year, remember this opinion article from the NY Times that talks about actions taken by Trump's Treasury in the lame-duck days of Trump's administration. I was once a proud Republican. But I'm ashamed of Republicans' support of Trump.
posted at: 08:42 | path: /general | permanent link
Sunday, November 01, 2020
Reading for the Undecided Voter
Two articles that every American ought to read. Maria Popova on Theodore Roosevelt's view of a good citizen and Peggy Noonan on why she will cast her vote for Edmund Burke.
posted at: 05:33 | path: /general | permanent link
Monday, August 24, 2020
Election Coming
Another excellent article that Trump supporters ought to read. Which, of course, they will not do.
posted at: 07:38 | path: /general | permanent link
Monday, May 18, 2020
Reading Before November
If you plan to vote in the 2020 presidential election (and I hope you do), you should read this article from Vox. It is about Trump and it is not positive. I tell you that so that you won't waste your time if you have decided to vote for Trump and nothing will change your mind. But maybe, just maybe, you are the very one who ought to read it.
posted at: 14:20 | path: /general | permanent link
Monday, May 11, 2020
COVID-19 versus Flu
You see a lot of nonsense on the web about COVID-19 and the seasonal flu. If you can read a graph, the image below ought to scare the crap out of you.
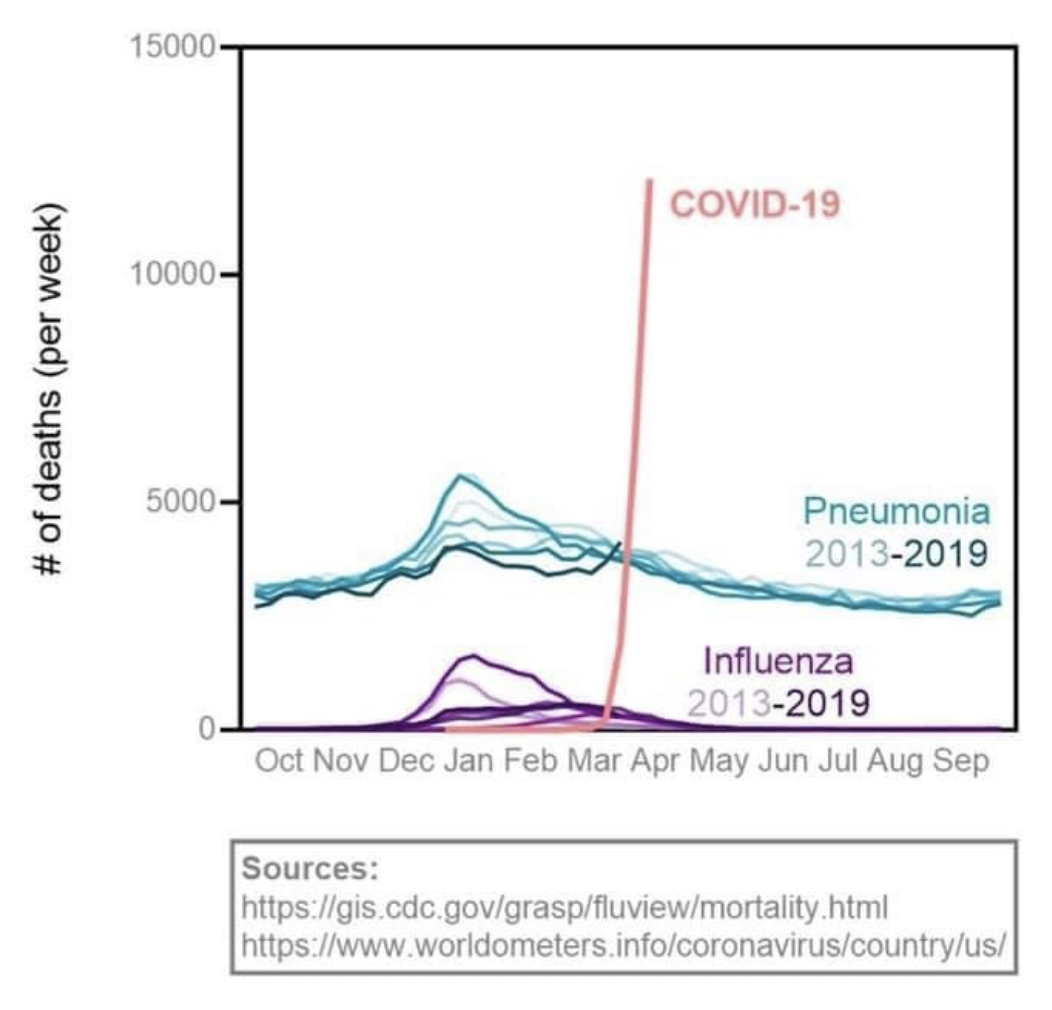
The image comes from one of Erin Bromage's blog posts. He is a trained and experienced infectious disease professor, so he is worth reading. In fact, his post on how SARS-CoV2 (a/k/a coronavirus) can spread in a community has gone viral because he is knowledgeable and writes clearly and thoughtfully.
posted at: 09:44 | path: /general | permanent link
Friday, May 08, 2020
Fake News?
At one time in America, when you listened to the evening news or read the daily newspaper, you could count on a clear distinction between news and editorials. You could count on almost all reporters to stick to facts or clearly state when they were quoting someone's opinion. No more.
To while away the time in grocery lines, I usually scan the covers of publications racked there. Years ago, I marveled that any sane person would buy the tabloids such as the National Enquirer as the stories were obviously not true. I now realize the tabloids have won. Mainstream news outlets resemble tabloids more than they do newspapers of 30 years ago. All media today compete for time (and clicks) with the uncontrolled opinion-spewing of social media. As a result, headlines--and even content--get more and more misleading.
How do you find news that you can rely on to give you the real story in this day and time? Two ways. One, keep up with the names of reporters you read, find ones that you believe give you the real story and read those more than others. Two, read news from multiple outlets. For example, if you're a conservative who usually listens to Fox News, tune to CNN to get the liberal view. And vice versa.
For the first way, if you are a conservative, as I am, I recommend Peggy Noonan. Although her columns are editorial, she underpins her opinions with fact. I also happen to agree with her opinions (usually).
For the second, a good web site that makes it easy to compare the news as reported from different viewpoints is Allsides. They attempt to characterize outlets as left, center, right and present the same story as reported by different outlets. It's not an exact science, but it makes it easier to compare viewpoints.
posted at: 09:17 | path: /general | permanent link
Saturday, April 11, 2020
Testing for COVID-19
What part of "people without symptoms can spread the disease" does Trump not understand when he says we do not need more testing?
posted at: 12:57 | path: /general | permanent link
Thursday, April 09, 2020
Kiplinger Article
Kiplinger's Personal Finance web site has an April 6 article entitled Filing My Taxes Early Cost Me My Stimulus Check. It's a technically accurate headline, but I hate headlines that are clearly designed as "click bait," worded to play on current fears to entice someone to check out the article. This one plays on the current concern about ensuring that you receive your fair share of the individual checks the U.S. government will be sending out ("the stimulus check"). Why do I feel as if this headline is "click bait"? Because it only tells one side of the story. Filing your taxes early could result in your getting a stimulus check that you would not have gotten otherwise. If your 2018 income was more than your 2019 income and you file early, your eligibility for a check will be based on your lower 2019 income. The author of the Kiplinger article just happened to have a higher 2019 income. His article does explain all the possible outcomes of when you file relative to the level of income in 2018 and 2019. But a fairer headline would have been, When You File Your 2019 Taxes May Affect Your CARES Stimulus Check.
posted at: 06:54 | path: /general | permanent link
Monday, February 03, 2020
New Computer
Excitement personified. I'm getting a new computer tomorrow, a Lenovo Thinkbook 13s. I've used Thinkpads forever. As I understand it, the Thinkbook is like a poor man's Thinkpad. I'll write about it after I get it and use it for a while.
My primary computer is my Macbook Pro. But I do some work that requires a Windows machine. When my Lenovo Twist died in 2018, I bought a "cheap" HP, thinking that I did not need much in the way of performance for the little work I did in Windows. Wrong! I've gotten too used to the speed of good laptops, so the HP seemed to crawl at times. It is a good computer, but with a Pentium processor and spinning disk hard drive, it was just too slow. So when Lenovo put the 2019 Thinkbook on clearance sale, it was just too good a deal to pass up.
The HP will be moved to being the file and print server on my home network. The computer that served that purpose, a Dell Inspiron 530 at 12 years old, will be retired.
posted at: 17:54 | path: /general | permanent link
Thursday, January 02, 2020
End of Support for Windows 7
Microsoft will end support for Windows 7 on January 14. I've put together a guide for upgrading to Windows 10. As of today, it is likely, assuming you have a valid product key for Windows 7, that you can still upgrade for free. We don't know if this will be the case after January 14, so you best get cracking.
posted at: 08:59 | path: /windows | permanent link
Tuesday, November 05, 2019
Notes on Alaska Trip
I started a separate blog for our cruise out of Vancouver up the Inner Passage to three Alaskan cities. You can find that blog here. As you will see if you go there, I posted very little, opting to tweet photos and short descriptions once we were aboard ship. You can find those on my Twitter page. I'll do better next trip. :-)
posted at: 06:33 | path: /travel | permanent link
Monday, August 19, 2019
Images in Microsoft Word
Can you make images in Word stay where you put them on the page? If you have ever inserted a picture or chart in a Word document and then continued to edit it, you have likely experienced your image, technically called an object in Word, jumping around. This occurs with any floating object.
Word has two types of objects: inline and floating. Inline objects stay where you put them, but you cannot flow text around them. They act like a single, big text character. They even change the line height of the line they are on. If you insert the object between two words on a line, the line will split there. If the object is narrower than the distance between the split point and the right margin, the rest of the line will be placed at the lower right corner of the object.
Floating objects are the ones that jump around. The reason they jump is because the paragraph to which they are anchored (attached to) moves to a different page. It may move to the previous page if text above the anchor paragraph is deleted. Or it may move to the next page if text was inserted above that paragraph. This "jumping" may occur even if you have the setting "Fix position on page" selected. Because that setting fixes the position on the page it is on, so if it jumps to the next or previous page, it will be at the same place on the new page.
So why do the objects move? Because the rule is that the object (picture, chart, SmartArt, shape, etc.) must be on the same page as the paragraph to which it is anchored. This rule cannot be changed. You can see which paragraph an object is anchored to by selecting the object: a small anchor symbol will be shown in the left margin. (If you do not see it, click the File tab on the ribbon, then select Options. In the Word Options dialog box, select Display from the left sidebar and click the checkbox beside "Object anchors" in the right pane.)
The anchor can be moved independently of the object by dragging and dropping the anchor on a different paragraph. Again, the paragraph must be on the same page as the object.
Here are two different strategies that minimize the chance of your object (e.g., a picture) moving.
Write all the text of your document and then insert your pictures where you want them.
Drag the picture to where you want it. Select the picture. Find its anchor. Drag the anchor to the first paragraph on the page so that if you add text or more pictures above that paragraph, it will have to move down the entire page before it flows to the next page and takes the picture with it.
Strategy #1 will definitely work since you will not be editing your text heavily after inserting your pictures. Strategy #2 will help, but the bottom line is that if you continue to edit your document after inserting the pictures, nothing will ensure that they will not move. But understanding that it's the picture being connected to a text paragraph that is causing the movement may help you minimize it.
posted at: 12:04 | path: /windows | permanent link
Friday, July 05, 2019
Windows 10 Guide
So many things have changed in Windows 10 since it was first released in 2015 that it is sometimes misleading to search the Internet for how to do something. Many times your search produces an article that seems to be spot on for your question. But when you try to implement it, it is actually describing a way to do it in an earlier version of Windows 10 and that way no longer works in the current version. A recent guide covers a lot of these things right now, at least up through the October 2018 version (1809) of Windows 10. Don't let the title of the guide, "100 common Windows 10 problems and how to solve them," fool you. Most of the items included are not "problems," just how to do things in Windows 10.
posted at: 09:02 | path: /windows | permanent link
Monday, July 01, 2019
Terminal commands for generating web pages for /blog folder:
//Change to directory where blosxom.cgi resides:
cd /Library/WebServer/CGI-Executables
//Run blosxom:
perl /Library/WebServer/CGI-Executables/blosxom.cgi -password='tige1300' -all=1
//If need to change timestamp on any files, open second Terminal window and:
cd /Library/WebServer/Documents/blosxom
//Change timestamp of desired file:
touch -t 201402091500 filename.txt
//Upload blog
rsync -av /Library/WebServer/Documents/blog/ jcb37310_jimsite@ssh.phx.nearlyfreespeech.net:/home/public/blog/
Need to eventually write a bash script to do this. UPDATE: completed 2019-05-03 13:26. Script name is blog.
posted at: 16:35 | path: | permanent link
Saturday, June 29, 2019
Blue Ridge Parkway
We went riding in the mountains along the Blue Ridge Parkway. The main reason for the drive was to see the Rosebay Rhododendron (white rhododendron) in bloom.  We saw lots of it on Highway 107 headed north from our Mountain Rest home and even more of it when we turned north on Highway 276 east of Brevard, NC. There's not a lot of it along the BRP, but we just love to ride along the Parkway and look at the spectacular views. We stopped at the Cowee Mountain Overlook and snapped this gorgeous sunset picture.
We saw lots of it on Highway 107 headed north from our Mountain Rest home and even more of it when we turned north on Highway 276 east of Brevard, NC. There's not a lot of it along the BRP, but we just love to ride along the Parkway and look at the spectacular views. We stopped at the Cowee Mountain Overlook and snapped this gorgeous sunset picture.
posted at: 15:00 | path: /travel | permanent link
Tuesday, May 21, 2019
New Search
I've added a new search box to each page on the site. I had been using Google's Custom Search. Of course the price for using Google is that it reserves the right to put ads in the search results. Also, Google only re-indexes the site on its schedule and new content may not have been indexed when you are looking for it. Now I'm using a Perl script hosted on my own site, so search is fast, always up to date, and the results have no ads.
posted at: 17:48 | path: /general | permanent link
Friday, May 17, 2019
TypeIt4Me and Terminal
If you use the TypeIt4Me text expander app on your Mac, you may have some issues with command entry in Terminal. Simply pausing TypeIt4Me while you are using Terminal eliminates the issue. BTW, other than that, TypeIt4Me is a wonderful app.
UPDATE 2019-05-21: TypeIt4Me support responded to my inquiry. It turns out you can tell TypeIt4Me to ignore specific apps. Go into TypeIt4Me's Preferences, click the Special tab, and add the app you want TypeIt4Me to ignore. Great! Solved my problem.
UPDATE 2019-05-24 09:26. The folks at TypeIt4Me support continued to look at the cause of my issue. This morning I got yet another email telling me they had figured it out. Under Preferences|AutoCorrect, I had the box labeled "Correct typos with AppleSpell" checked and this was causing the problem. Since I want to keep this setting, I left Terminal in the list of apps that TypeIt4Me should ignore. Hat tip to Guy and Riccardo at TypeIt4Me for great technical support!
posted at: 12:55 | path: /mac | permanent link
Thursday, May 16, 2019
More CLI Tutorials
If you went through Zed Shaw's Command Line Crash Course, you saw that it only covered a limited number of commands. If you are like me in this age of "free" information, you go through several tutorials to find that one that matches your idea of the right level of detail and the right presentation. Here are several more free CLI tutorials that I found useful:
- Lifehacker's A Command Line Primer for Beginners,
- Lifehacker's Become a Command Line Ninja With These Time-Saving Shortcuts, and
- Learn Enough Command Line to Be Dangerous.
Comments on Tutorials
If you liked the "learn the hard way" (i.e., memorize progressively more difficult concepts and practice, practice, practice) approach of Zed Shaw, you might be interested in some of his other tutorials on programming. Most of these have a fee.
Also, the third tutorial listed above, Learn Enough Command Line to Be Dangerous, is very complete and detailed. Recommended.
posted at: 11:34 | path: /bash | permanent link
Wednesday, May 15, 2019
Keyboard Shortcuts for Terminal
These shortcuts apply to macOS Terminal. They may work in other bash shells, but I don't know.
^ = control key
^A - move cursor to beginning of line
^E - move cursor to end of line
^U - delete from cursor to beginning of line
^K - delete from cursor to end of line
^R - search command history. Press again to find next.
cd - - toggle between paths
!! - paste last command
!<command name> - repeat last command using <command name>
!$ - paste arguments from last command
^<text>^<replacement> - replace <text> in last command
posted at: 11:27 | path: /bash | permanent link
Tuesday, May 14, 2019
Strange Terminal Behavior
I'm using Mojave 10.14.5 on a 2017 Macbook Pro. In Terminal, when I type the command popd, as soon as I press Return or Space, the following is added to the end of my command:
;2D;2D;2D;2Ddopp
The pop command works, but I also get this output:
-bash: 2D: command not found
-bash: 2D: command not found
-bash: 2D: command not found
-bash: 2Ddopp: command not found
This also happens with the dirs command. Is this normal behavior for Terminal? If not, how can I fix it? If you know, please send me an email by clicking Comment in the left sidebar.
UPDATE 2019-05-21: I traced the problem to the text expander TypeIt4Me. Their support responded to my inquiry and advised me to use Preferences|Special to tell TypeIt4Me to ignore (i.e., not expand) Terminal. That solved my problem.
They continued to work on the issue and found that if the box labeled "Correct typos with AppleSpell" under Preferences|AutoCorrect is checked, AppleSpell will correct things in Terminal.
posted at: 08:34 | path: /bash | permanent link
Monday, May 13, 2019
Climbing the Tree in bash
If you are going through Zed Shaw's Command Line Crash Course, you see that much of his content relates to changing from one directory to another and knowing where you are in the directory tree. Using the command line is so different from using a GUI such as Finder to navigate the directories. With Finder, you see the directory tree displayed and all you have to do to move from one to another is click.
Bash shells on other versions of Linux/Unix have a terminal command "tree" to show you all the directories "below" your working directory. MacOS does not come with tree installed. You can, however, install it yourself. A post on SuperUser tells you how to install the tree command on macOS.
posted at: 17:51 | path: /bash | permanent link
Friday, May 10, 2019
Flash Cards
Shaw's Command Line Crash Course correctly says you must memorize bash/Terminal commands to effectively use them. He further suggests that you make up flash cards to help you do that. If you want an on-screen alternative, Quizlet already has cards to learn macOS Terminal commands.
posted at: 10:21 | path: /bash | permanent link
Another Peggy Noonan Gem
Recommended reading. Republicans in a Nation Needing Repair.
posted at: 08:47 | path: /reading | permanent link
Thursday, May 09, 2019
Zed Shaw's CLI Tutorial
In an earlier post, I recommended that beginners go through Zed Shaw's Crash Course to hone their basic skills in using the command line. If you use macOS and are doing Exercise 7, you may get a message that the directory you are trying to remove using rmdir is not empty. rmdir can only delete (remove) an empty directory. The reason the directory is not empty is that you may have used Finder to display the directory, resulting in Finder creating a hidden file holding its settings.
At the bottom of the list of commands to practice for Linux/macOS, Shaw provides a warning about and instructions if you get the "not empty" message. He recommends that you use rm -rf <dir_name> instead of rmdir. That works. But Shaw does not explain that the -rf switch requires care because you are telling macOS to remove (delete) without confirmation the directory and all of its subdirectories (i.e., the -r switch means to recurse through all subdirectories). If you mistakenly type rm -rf /, you will delete every directory on your hard drive. So be very careful with rm -rf <dir_name>.
posted at: 09:57 | path: /bash | permanent link
Wednesday, May 08, 2019
bash on Windows
Several years ago, Microsoft added the Windows Subsystem for Linux to Windows 10. This allowed you to add what is in essence a Linux-type terminal app and be able to execute Linux commands and run Linux programs on a Windows computer. This is neat for my current effort to learn to use the bash shell and scripting. Now Microsoft has announced even wider support for Linux/Unix type programming with the Windows Terminal. So learning bash shell scripting will be useful on either a Windows, macOS, or Linux driven computer. Expected by the end of 2019.
posted at: 10:07 | path: /bash | permanent link
Tuesday, May 07, 2019
CLI
My first home computer was a Tandy Radio Shack TRS-80. It used a cassette tape (yep, just like the ones you played music from) to store its programs. 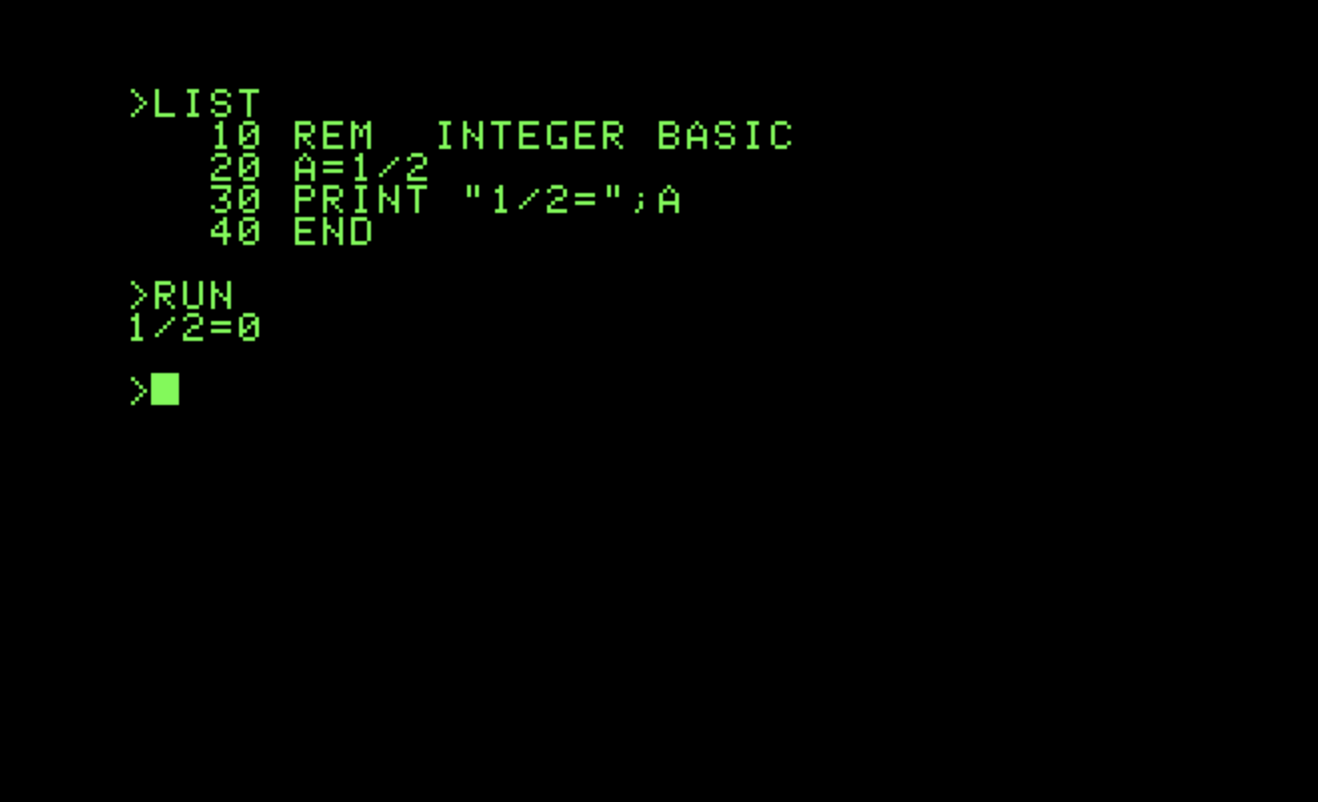 When you turned it on, you were presented with a prompt and a blinking cursor, ready for you to type something. I could not find a screenshot of that, but I did find one for the opening screen of the Apple II, which came out the same year, 1977. The TRS-80's prompt was similar because they both used the programming language BASIC as the operating system.
When you turned it on, you were presented with a prompt and a blinking cursor, ready for you to type something. I could not find a screenshot of that, but I did find one for the opening screen of the Apple II, which came out the same year, 1977. The TRS-80's prompt was similar because they both used the programming language BASIC as the operating system.
Even when I "graduated" to the IBM PC in 1981, turning it on brought you to an empty screen with only A:\> (designating one of the two floppy disk drives, A and B) and a blinking cursor. This is the command line interface (CLI)--no icons or menus in sight. The computer expects you to type a command to get things started. A program is running in the background to interpret your commands to the operating system and start the computer to doing what you told it to do. Thus CLI is sometimes called command language interpreter. When you are not familiar with the commands, that blinking cursor fosters all sort of anxiety.
In my blog, I talked about my experience with the Windows command line and batch files (Windows version of scripts). I'm exploring how to write scripts to do repetitive tasks on my Macbook Pro. The scripts are a series of commands in a text file that can be run from the CLI prompt by typing the name of the file. The shell for macOS is a program called bash, an abbreviation of "Bourne again shell." So before I can write a script consisting of commands, I need to know what those commands are and how to use them. The best resource I have found on the Internet is Zed Shaw's Command Line Crash Course. So if you are interested in learning along with me, go through that tutorial and then we will proceed to scripting the commands.
posted at: 11:45 | path: /bash | permanent link
Monday, May 06, 2019
Still Hanging on to Windows 7?
According to current statistics, about 45% of Windows' users continue to use Windows 7. If you are one of those, you might want to read about the security shortcomings of Windows 7 relative to Windows 10. If you are an average home user as I am, you won't understand a lot of the acronyms and technical nuances of that article. But the clear message, just from the number of areas that the security experts that wrote it cite, is that Windows 10 is way more secure than Windows 7. For home users, security support for Windows 7 will end on January 14, 2020. Besides, you can still upgrade from Windows 7 to Windows 10 for free. Time to upgrade.
posted at: 06:54 | path: /windows | permanent link
Thursday, May 02, 2019
Jim and Debbie's Travel Log
Posts about our travel are sprinkled throughout my blog. You can filter the blog to see only the travel-related posts. The posts contain a picture or two to illustrate the descriptions. Check my Twitter page for more pictures.
posted at: 10:16 | path: /travel | permanent link
Wednesday, May 01, 2019
bash Scripting
As I've said before in this blog, I used Windows almost exclusively for 30 years before buying a Macbook Pro, which I use almost exclusively now. I got pretty good writing Windows batch (aka cmd) scripts to do things on my computer that I did repetitively. For macOS, I need to learn to write bash scripts to do these things. I'll post what I learn as I go along, so come back to join me if you are interested in watching an absolute beginner in bash try to figure this out.
posted at: 10:14 | path: /bash | permanent link
Saturday, April 27, 2019
Still Spending
Back in July of 2011, I blogged about government spending versus tax receipts. The article that I linked to in that post no longer exists, so I went looking for an update of the key graph. You can review the updated graph of tax receipts and spending as a percent of gross domestic product. Note that since the recession in 2008, our government constantly spends more than it receives. Is this any way to run a "business"?
posted at: 19:20 | path: /general | permanent link
Tuesday, April 23, 2019
New Way to Generate Web Pages
I am changing to generating my web pages using Blosxom. Blosxom is a Perl script that takes care of generating and organizing weblog posts. It is lightweight and fast. Best of all, it allows me to generate my weblog pages locally on my Macbook Pro and then upload static HTML files to my hosting service. This saves me a little bit of money as my hosting service charges less if I don't use the scripting languages on its server.
posted at: 08:38 | path: /www | permanent link
Wednesday, March 13, 2019
October 2018 Windows 10 Update
Yesterday I finally got the version 1809 update delivered to my computer. This version was initially released on October 2, 2018. But, there have been some problems.
Shortly after Microsoft first released 1809, reports of the update deleting files on users' computers began to surface. Microsoft pulled the update back on October 6 because of these reports. In tracking down the problem, Microsoft found a glitch in its update process.
A user of the Home version of Windows 10 (most of us) has little control over when Microsoft automatically updates a computer. In the Update & Security section of the Settings app (accessed by pressing the Windows key and I simultaneously, then clicking on Update & Security), a user can manually get the latest updates by clicking the "Check for updates" button. (It is not necessary to do a manual update; Microsoft will, on its schedule, automatically send updates to your computer.) The process glitch Microsoft found was that using the "Check for updates" button for 1809 bypassed some of the "ready to receive update" checks of your computer that occurred if Microsoft was automatically updating your computer in the background. The result was corrupted updates and computers that did not work.
It took some time to fix this and Microsoft did not re-release 1809 until November 13. Even then, Microsoft released it only to a small number of expert users to ensure everything was right this time. As a result, most home users did not begin to receive this update until mid-January 2019. I chose to wait until Microsoft automatically updated my computer.
In a way, this is good news for home users of Windows 10. All of the problems with 1809 have caused Microsoft to review all of its testing and release procedures. This should result in more reliable updates in the future for all of us. You can check the version your computer has by opening the Settings app, clicking the System icon, scrolling down the menu on the left of the page to the About menu item and clicking on it. On the right side of the screen, scroll down to the "Windows specifications" section and read your version number.
posted at: 09:54 | path: /windows | permanent link
Saturday, January 26, 2019
Walt Disney World
Today started a six-day stay at Disney World with two of our grandchildren (and their parents :-)). Allison made all the arrangements. We stayed at the Art of Animation Resort and used mostly bus transportation from the hotel to the parks. Pleasant to leave the driving to someone else. This was my first trip in 25 years so I was looking forward to the changes.
Today was Magic Kingdom. The constant rain did not keep us from following Allison's plan. Not a lot of changes in the rides we did today except for updating. Space Mountain is still my favorite and turned out to be one of Claire's.
 Next day the rain stopped and we were at Animal Kingdom. Lots of changes here in 25 years. Pandora - The World of Avatar is, of course, completely new. The new ride Avatar Flight of Passage had a two-hour wait today, so Greg, Alex, and I came early on Thursday to ride it. It is now my all-time favorite ride at Disney. Alex liked it too.
Next day the rain stopped and we were at Animal Kingdom. Lots of changes here in 25 years. Pandora - The World of Avatar is, of course, completely new. The new ride Avatar Flight of Passage had a two-hour wait today, so Greg, Alex, and I came early on Thursday to ride it. It is now my all-time favorite ride at Disney. Alex liked it too.
Tuesday was Hollywood Studios. Lots of Star Wars and Toy Story stuff here. The Tower of Terrors was my favorite here although Slinky Dog Dash roller coaster was a close second.
Wednesday we were at Epcot. Lots of new here, too. Twenty-five years ago, it was mostly "educational" exhibits. Now there are lots of rides. Soarin' was my favorite although Test Track was a close second.
Thursday we re-visited Animal Kingdom while the girls went shopping. Debbie and I had dinner in Monsieur Paul in Epcot. Very upscale and very French.
Friday we hit both Magic Kingdom and Hollywood Studios to catch some of rides we had not had time for earlier in the week.
One of the big changes at Disney World since my last visit is with fireworks and parades. As best I remember, there was one big fireworks show, one laser light show, and one big parade 25 years ago. Now there are parades and fireworks in every park. The fireworks are now in the context of a monstrous-sized film projected on the sides of buildings and a laser light show coordinated to the film and the fireworks.
Hated to go home, but it was a great week!! According to Debbie's Fitbit, we walked 51 miles. Enjoyed every step of it.
posted at: 21:45 | path: /travel | permanent link
Sunday, January 13, 2019
California
After attending the college football National Championship game in Tampa two years ago, I did not plan to attend this year's game. But once Clemson made the game again, Debbie and I decided to go. After all, how many more of these will the Tigers play in during my lifetime? So we flew to San Jose on Saturday, January 5.  We stayed in Mountain View and scouted the area on Sunday and Monday and went to the game Monday night at Levi's Stadium in Santa Clara, home of the 49ers. Tigers demolished Alabama 44-16. National Champs again, twice in past three years. Amazing.
We stayed in Mountain View and scouted the area on Sunday and Monday and went to the game Monday night at Levi's Stadium in Santa Clara, home of the 49ers. Tigers demolished Alabama 44-16. National Champs again, twice in past three years. Amazing.
Tuesday we drove over the Santa Cruz Mountains, then down California Highway 1, the Pacific Coastal highway, to Pebble Beach. This picture, my favorite from the trip, is of the Lone Cypress that is emblematic of Pebble Beach. Beautiful scenery along this drive. See the Twitter account for more photos. We relocated to American Canyon, just south of Napa, for the rest of the week's stay.
Wednesday and Friday were wine days. We took a guided tour of Napa Valley on Wednesday. Had a good guide, therefore a good tour, and bought some expensive (by our standards) wines that we had shipped to Aiken. Thursday was supposed to be a guided tour of San Francisco, but we did not feel well and skipped it, opting to ride around and see more of Napa Valley on our own. Friday was a self-guided tour through Sonoma Valley. Beautiful vineyards everywhere.
Saturday we drove to San Francisco and saw Fisherman's Wharf, Lombard Drive, and the hilly streets. We stayed in San Jose so that we could more easily make our flight Sunday morning. What a great week!
posted at: 22:11 | path: /travel | permanent link
Friday, September 28, 2018
A Busy 2019
2019 is shaping up to be a busy travel year for us. We already plan to go to the CFB National Championship game in Santa Clara, CA, in early January if the Tigers make it.  Later in January a trip to Disneyworld is on the books. And we're thinking about that Alaska cruise we've always wanted to go on. Oh well, that still leaves the last half of the year. UPDATE 09/28/2018: the Alaska cruise is booked for September 3 through 10. We plan to take the train from Skagway (see the picture).
Later in January a trip to Disneyworld is on the books. And we're thinking about that Alaska cruise we've always wanted to go on. Oh well, that still leaves the last half of the year. UPDATE 09/28/2018: the Alaska cruise is booked for September 3 through 10. We plan to take the train from Skagway (see the picture).
posted at: 08:00 | path: /travel | permanent link
Monday, August 06, 2018
Your Browser Says the Page is Not Secure
We have all heard the stories of a bank account being cleared out because a hacker convinced the owner to enter personal and account information in a fraudulent website. Ransomware, where a hacker encrypts the files on your computer and then demands money to release them, gets more and more publicity. We are justifiably wary when our browser, whether it be Chrome, Firefox, Safari, Opera, Internet Explorer, or Edge, pops up a message that the web page we are visiting is not secure. But just what does that "not secure" message mean and what action should we take when we get it?
Let's take a step back and talk about how your computer connects to the Internet. We are not talking about your service provider (such as Atlantic Broadband) or whether you connect with a cable or wi-fi. We are talking about the procedure or protocol your browser uses to exchange information between your computer and a computer on the Internet.
When the World Wide Web (WWW) was invented in 1989 there was only one protocol, HyperText Transport Protocol or HTTP. Under this protocol, information -- both the text and images a web page sends you and text and images you might send to a web page -- is sent in its raw, unencrypted form. For example, when you enter your password to sign in to an HTTP site, your browser sends it to the web page in plain text (even if your browser covers it with dots as you type it). Consequently, anyone "watching" your communication, that is, a hacker, can read your password.
It was not long before web site owners realized that they needed an additional protocol to transmit confidential information securely, that is, encrypted or put into code. Thus Secure HTTP, better known as HTTPS, was invented. HTTPS uses additional steps in the communications between computers, called a secure socket layer or SSL. These extra steps do two things: encrypts the information sent between your computer and one on the Internet and requires that the web site have a certificate that verifies that the site is who it says it is. The certificates are issued by companies that have established that they can be trusted. You can imagine that it would not take but one incident of a hacker getting around a given company's certificate to eliminate that company from being considered by other web sites.
Many web sites still use HTTP, as indicated by the site's address beginning with http:// in the address bar at the top of your browser window. Banks, credit card companies, financial companies, pharmacies, and any other site that wants the information exchanged to be confidential use HTTPS, as indicated by https:// at the beginning of the address. An https:// site also has an image of a padlock in the address bar indicating it is secure.
Because incidents of identity theft and other hacker-related crimes are increasing, the major browsers (Chrome, Safari, etc.) began last year to display a "not secure" message if you were asked to enter information, such as a password or credit card number, on an HTTP web page. It has always been good practice before sending confidential information to a web page to be sure that the page address begins with https:// and that the padlock image is displayed. The browser makers just started doing this for you by displaying a "not secure" message when the input form is on a page with an http:// address.
So if HTTPS is more secure, why don't all web sites use it? Two reasons: those extra steps of encrypting the communication and money. The extra steps take time and thus an HTTPS web page loads a little slower than an HTTP page. The SSL certificates must be purchased from one of the trusted certificate authorities by the site owner, so an HTTPS site costs more to operate.
There are, however, companies, such as Google, that want to see all web sites use HTTPS. So this month, Google is changing the latest version of its Chrome web browser to display a "not secure" message for any web page that uses HTTP. The other major browser makers will likely follow suit in the future.
What should you do if you get a message from your browser that a web page is "not secure"? Ask yourself whether you care if a hacker could read the information you are sending or receiving from the web page. If the information is not confidential and you do not care, ignore the "not secure" message. If the information is confidential and you do care, close that web page. And if it's your bank's page, call them and tell them about it.
posted at: 10:32 | path: /www | permanent link
Friday, May 25, 2018
April 2018 Windows 10 Update
On April 30, Microsoft released another major update to Windows 10, the April 2018 Update. This is the fifth major update, called a feature update by Microsoft, since Windows 10 was originally released on July 29, 2015. The previous four updates were the November Update (November 2015), Anniversary Update (August 2016), Creators Update (April 2017), and Fall Creators Update (October 2017).
As with earlier major updates, it may take several months before everyone's computer is updated, although this update appears to be rolling out to home users faster. You can go to Microsoft's web site (http://bit.ly/mcg_wdl) and update immediately or you can wait for Windows Update on your computer to get around to you.
Before Windows 10, Microsoft released a major version upgrade about every 3 years: Vista in 2007, 7 in 2009, 8 in 2012, and 10 in 2015. Microsoft announced that Windows 10 would be the last version of Windows and would be updated "as a service." The intent is to keep Windows 10 up to date almost continuously through frequent feature and security updates. Most security updates occur on "Patch Tuesday," the second Tuesday of each month (although they can occur at any time). The major feature updates, such as the April 2018 Update, occur in the spring and fall.
The "Patch Tuesday" updates change a small part of the code for Windows 10. Consequently, they are small downloads. The feature updates are essentially a re-publication of the entire code. That results in a download of 3 to 4 gigabytes (GB), a big download that takes a long time, usually hours, to download and install. Last year, Microsoft began to change the way feature updates are downloaded and installed on your computer to speed up the process. The April 2018 update enhances those changes, so you should be able to get back to work on your computer even faster than before.
So what are the changes in the April 2018 update? For home users, the most visible change is Timeline. This is an addition to Task View, the current feature that displays thumbnails of all the open windows and allows you to pick the window you want to make active. Timeline adds a history of all the actions you have taken on your computer, all the web pages you have visited, all the files you have edited, all the pictures and videos you have looked at. By default, Timeline shows you what you did during the past 7 days. You can change that to 30 days.
You invoke Timeline by clicking the Task View taskbar icon (looks like a rectangle with a smaller rectangle attached to each side), or by pressing the Windows key and the Tab key together. Currently, Timeline only shows the actions you took using Microsoft programs such as Edge, Word, Excel, Wordpad, etc. It will be up to other program developers to modify their applications to provide input to Timeline. Whether developers will do so depends on consumers. If consumers are enthusiastic about Timeline, developers will update their programs to use it.
If you use Cortana on iOS or Android, Timeline will even show your activities on those devices as well. This will allow you to start looking at something on your phone while you're out and about and continue on your PC when you get home.
Focus Assist is an enhanced, renamed feather which allows you to quickly shut off notifications and other interruptions while you're working on a project on your PC that requires your undivided attention. Focus Assist was called Quiet Hours in earlier versions of Windows 10.
Window 10's default browser, Edge, has been improved. One of the best additions allows you to quickly silence audio from a video automatically played on a web page when you go to it. Edge will show an icon on the page tab to allow you to see which page is producing sound. You can quickly silence the audio by right clicking the tab and clicking "Mute tab." No more frantically searching the web page for the video that is making all that noise that you do not want. You can print web pages from Edge with less clutter. The "hub" where your browsing history and favorites are displayed also received changes to the interface to make navigating cleaner and faster.
Microsoft continues to enhance Cortana, the talking personal assistant, expanding the areas it can help you with.
The April 2018 update includes a feature to share files with nearby devices, similar to Apple's AirDrop. The sharing is done using Wi-Fi or Bluetooth and is relatively easy to set up. The update includes improvements in pairing devices with your PC using Bluetooth. There are many other minor improvements to the user interface of Windows 10 and lots of stuff "under the hood" to make your PC experience more secure.
posted at: 13:47 | path: /windows | permanent link
Saturday, May 12, 2018
Should You Disable Javascript?
In a class I was recently taking, we went to a known safe web site to cut and paste some text to work with in the class. The web site, as almost all web sites on the Internet do these days, used Javascript. One of the students could not load the web site because she had been advised by someone to disable Javascript in her web browser as a security precaution. Is this necessary?
In a word, no. But that's not the whole story. Javascript can possibly be used to invade your computer and you do need to be aware of how and how to protect yourself. Here is a good summary article about protecting yourself against Javascript malware. It gets a little technical, so I'll summarize its advice:
- Keep your browser, any extensions you use within it, and your operating system, whether Windows or macOS, up to date.
- Be suspicious of any link in an email or text. Make sure the link goes where you think it does by hovering your mouse pointer over it and checking that the address displayed in the popup line in your email program is the same as where the email says it is. Even then, don't click on a link in an email unless you believe it is safe.
- Run anti-malware software on your computer and keep it up to date.
- Never click on an attachment to email unless you know who it came from and trust them. Even then, if you were not expecting an attachment, confirm with the sender that they really sent it.
- Disable Flash and Java in your browser and operating system. (Java and Javascript are two separate, different, unrelated things.)
Yes, that's a lot of work. It's the price of enjoying the Internet today.
posted at: 08:10 | path: /www | permanent link
Wednesday, April 25, 2018
Reading
I recently read Factfulness: Ten Reasons We're Wrong About the World--and Why Things Are Better Than You Think by Hans Rosling. If you have never seen one of Rosling's TED presentations of world stats, you ought to go watch one. They are entertaining and enlightening. This book is also. Highly recommended.
posted at: 08:16 | path: /reading | permanent link
Tuesday, April 17, 2018
Windows 10 Info
I keep notes on questions (and my answers) that people asked me about Windows 10 in a course that I used to teach. There are also some links to Windows 10 information on the web. You can go here to see them.
posted at: 14:05 | path: /windows | permanent link
Monday, April 02, 2018
Basics of Clearing a Browser Cache
If a frequently updated web page that you visit does not appear to change between visits, your browser may be loading an older version from your browser cache. If you also use a publicly-available computer, such as at a library, to access a secure site, some of your information may remain recorded on that computer when you stop using it. To remedy these situations, you may need to clear your browser cache. This post tells you how.
Most of us use one of the major modern browsers to access the Internet: Chrome, Internet Explorer, Firefox, Opera, Safari, or Edge. We also know that sometimes we need to refresh or reload a web page to make sure we are viewing the most up to date version. All of those browsers have the same icon to refresh or reload a page: a broken circle with an arrowhead on one side of the break. Click that and the page reloads. You can also refresh the page with a keyboard shortcut: F5 for the Windows browsers and Command and R keys pressed simultaneously for Mac browsers. But sometimes when you refresh a page that you know has been recently updated, the displayed content does not change. What's up with that? The culprit is the browser cache.
The Internet truly is an amazing thing. Using it, you can sit in your den and read a web page on a computer anywhere in the world. Click on a link in your browser and communications between your browser and the web page begin at, literally, the speed of light. Usually in a matter of seconds, the browser and server (the computer on which the web page resides) talk to each other multiple times to establish that you want to look at a specific page (specified by the link), that the server is who it says it is, and that everything is in place for the server to send all the text, graphics, and videos on the page to your browser, which displays the web page. Amazingly fast. But what if it could be faster?
That's where the cache comes in. The cache is a file on your hard drive that saves all the communications between your browser and the server. Even though the Internet is fast, it is not as fast as retrieving text, graphics, or videos from your hard drive. If you revisit a web page, your browser first checks to see if the information for that page is in the cache. If it is, it loads the page from there and delivers the web page to your screen. The page will be loaded faster than if it was loaded from the server on the Internet.
The problem occurs when the information on the Internet server has changed, but the version in your cache has not. Then, even if you reload the page, it reloads the unchanged version from the cache. So you don't see the changes on the server. The way to resolve this is to delete the version in your cache. This is called clearing the cache. When you click on the page's link after clearing the cache, the page as it exists on the server downloads to your browser. Clearing the cache is done from within the settings of your browser. Each browser has a slightly different way to do it. Here is an article that tells you how to clear the cache in all the major browsers.
You want to be careful what you clear from the cache. As noted above, all the communications between the server and your browser are stored in the cache. This includes cookies, passwords, and your browsing history (a list of all the web pages you have visited). You probably do not want to delete some of that information from your cache as it includes information that you will have to reenter. Each browser allows you to select what information you delete (clear) from the cache. For the outdated web page, you should selectively delete information labeled "page data" or "images and files" or "temporary Internet files." You will then be assured of getting the most recent version of the web page downloaded to your browser.
posted at: 09:51 | path: /www | permanent link
Thursday, March 08, 2018
Who to Read?
It's hard to get thoughtful, unbiased coverage of what's going on in our federal government these days. The "mainstream media" is generally liberal. But I want to read a conservative, Republican viewpoint from a writer who works to present a balanced, objective story. If you're like me, try reading Peggy Noonan. She was Reagan's top speech writer and continues to provide thoughtful opinions about government.
posted at: 09:31 | path: /reading | permanent link
Tuesday, January 23, 2018
Who Were the Original Programmers?
With all our devices today--computers, tablets, smartphones--we depend on computer programmers to write the code that allows us to do incredible, complex things. The world now seems to run on computer code. What do you see in your mind's eye when you think about a computer programmer? I'm guessing most of us visualize a young man, mathematically inclined, who might tend to be a loner, spending days and nights on end pounding a keyboard to turn out some new app or game. That is probably a reasonable picture of today's primary computer programmer. But it may surprise you to learn that the original computer programmers were all women.
At the beginning of World War II, the demand for artillery firing tables was increasing exponentially. Firing tables tell the artillery gunner in the field how to aim his gun to hit a distant target. For every angle of elevation of the gun barrel, every wind speed, every range to the target, there were numerous trajectories that an artillery shell could take.
Each of these trajectories required thousands of calculations to produce a firing table for a particular type of gun. The U.S. Army decided to hire women to make these calculations (which were viewed as "clerical" work and more suitable to women than men) and embarked on a nationwide recruitment program for college-educated, mathematically-talented women. They came to be called "computers" and hundreds of them manned hand adding machines in large rooms to produce the firing tables.
The problem was that it took too long to solve the differential equations to calculate the trajectories using adding machines. So the Army funded a project at the University of Pennsylvania to build an electronic calculator to produce the firing tables faster. The calculator, the first electronic computer, was called ENIAC (electronic numerical integrator and computer). It was designed and built by John Mauchly and Pres Eckert and the team of engineers and technicians at Penn.
After ENIAC was built, it still had to be "programmed," set up to solve the equations for the trajectories of an artillery shell. There were no instruction books on how to program it. More difficult, programming was accomplished by setting switches and plugging wires so that the machine processed the math in the correct sequence. The programming was turned over to six of the "computers" who had been calculating the firing tables by hand: Kay McNulty, Betty Jennings, Betty Snyder, Marlyn Meltzer, Fran Bilas, and Ruth Lichterman.
The women were given blueprints of ENIAC's wiring and charged with figuring out how to produce firing tables from this monster (ENIAC weighed 30 tons and occupied a 30x50 foot room) of a computer. And they did, becoming the first computer programmers and developing many of the basic techniques still used today in modern programming languages, such as COBOL, developed by another woman, Grace Hopper.
Sadly, after the war, when the amazing accomplishments of ENIAC were publicized, the women who had made it work were not mentioned. They were not even invited to the dinner celebrating the success of ENIAC, even though they stayed long into the night to fix a glitch that threatened to derail a successful demonstration to the Army brass.
These women led the way for other female programmers. Indeed, into the 1960s, most computer programmers were women. Who knows, if the pioneering work of the "ENIAC Girls" had been widely publicized to serve as role models and inspiration, that may still be the case today.
posted at: 09:25 | path: /general | permanent link
Friday, December 08, 2017
Which is Better: Mac or PC?
If you type this article's title into an Internet search engine, be prepared to enter a "holy war" in which proponents of each type of computer will passionately bombard you with reasons why one is better than the other. We're going to try to stay objective and factual in this article to give you information to help you decide for yourself. I am a long-time Windows user. Four months ago, I bought a MacBook Pro. This article is basically my personal experience with my purchase.
My journey to the Mac started with an iPad. The volunteer organization at which I teach had begun in 2013 to offer courses about using an iPad. I mentioned to my wife that I probably should get one to keep up with what we were teaching. I was half-kidding. But when my birthday rolled around, she presented me with an iPad Air 2. I was impressed with its performance, smooth scrolling, and the downright beauty of its display. When my old Android phone died, and having watched with envy at how the battery lasted on my wife's iPhone, I decided to get an iPhone.
I am a software geek. When I get a new gadget, I want to understand how its software works and how I can use it to get work done. The hardware interests me less; I just want it to support the software and perform well. I have been using personal computers for more than 30 years. Most of them ran DOS in the early days and Windows since version 3.11 was released in 1993. These new computers -- iPhones and iPads are just small computers -- were a lot different in how they used software.
The one thing that stood out to me was how seamlessly the iPhone and iPad communicated with each other. You can make a Windows PC and an Android smartphone or tablet (or even an iPhone or iPad) communicate with each other, but that's the rub: you have to "make" them communicate. They don't do it when you take them out of the box and turn them on. That seamless communication should not have surprised me. The advantage Apple has is that it produces both its hardware and software. It is easier for them to design their products to talk to each other from the start.
With the iPad and iPhone, I could enter a note or a calendar appointment in one device and have it show up in the other. Almost every app on the devices was set up to communicate like this. Yes, I had my Windows PC set to communicate with my Android smartphone through Google, but that's the point. I had to use Google, install Google programs on both devices and set them up to communicate. The iPhone and iPad just did it.
My Windows PC is a 2012 model that came with Windows 8 installed. Doesn't seem that old, does it? But when Windows 10 was released in 2015, there were minor incompatibilities with my hardware. Windows 10 is a wonderful operating system, designed to make use of the latest in hardware, some of which is not yet even being manufactured. But it does not necessarily play well with older -- even just 3 years older -- hardware. The minor performance issues, which an average user may not even notice, grated on me every time I used it. So I decided to buy a new computer. My experience with how easily the iPad and iPhone communicated led me to consider a Mac.
On the surface, deciding between a PC and Mac appears to be a "no brainer." A home PC costs about half of what a Mac with comparable hardware specifications costs. What do you get in a Mac for that extra cost? First, a Mac is better built than most PCs. PCs come from different manufacturers in a highly competitive marketplace, so cutting costs to the bone is a priority. (Note: those manufacturers also produce computers built just as good as a Mac, but they cost as much or more than a Mac and are mainly built for business, not home, use.) Second, a Mac comes with all the software you need to get work done. For example, you don't have to lay out another $100 to $400 dollars to get a high-performance word processor, spreadsheet program, and presentation software. Third, the Mac display screen, especially the Retina models, is just beautiful to look at. If you sit at a computer for several hours a day, you will appreciate the sharper fonts and brighter colors. Your eyes simply will not be as tired at the end of the day.
I'm really happy with my MacBook Pro. I still use my Windows machine a lot because I developed shortcuts over the years to help me get things done faster. But I will say this: when I reach for a computer to read the news over a cup of coffee in the morning, more and more I'm reaching for the Mac.
posted at: 11:44 | path: /mac | permanent link
Sunday, October 22, 2017
Windows Fall Creators Update
On October 17, Microsoft released the Fall Creators Update to Windows 10. This is the third major, named update since Windows 10 was originally issued on July 29, 2015. The previous three updates were the November Update (November 2015), the Anniversary Update (August 2016), and the Creators Update (April 2017). As with earlier major updates, it will take several months before everyone is updated.
Before Windows 10, Microsoft released a major upgrade about every 3 years: Vista in 2007, 7 in 2009, 8 in 2012, and 10 in 2015. Microsoft announced that Windows 10 would be the last version of Windows released and would be updated "as a service." The intent is to keep Windows 10 up to date almost continuously through frequent feature and security updates. Most of these updates occur on "Patch Tuesday," the second Tuesday of each month. In the future, the major feature updates will occur about twice a year, in spring and fall.
The "Patch Tuesday" updates are incremental updates that change only a small part of the code for Windows 10. Consequently, they are not large downloads to your computer. The major, named updates so far have been essentially a re-publication of the entire code of Windows 10. That resulted in a download of 3 to 4 gigabytes (GB), a big download. In the Creators Update of April 2017, Microsoft announced that even the major updates would be incremental, downloading only the changes to the Windows 10 code. The upcoming Fall Creators Update will be the first major update since that announcement, so we will see how much smaller the download is.
In any event, if your Internet connection has a limited data plan (for example, through a personal "hotspot" on your cell phone or a prepaid data plan such as Walmart's Straight Talk or a satellite), you should make sure it is set to a "metered" connection. To check or change the setting, do the following steps while you are signed into Windows with an administrator's account. Open the Settings app by pressing the Windows key and the letter I at the same time. Click the icon labeled Network & Internet and then click the link labeled "Change connection properties" under Network Status. The toggle switch labeled "Set as metered connection" should be On. (Note: if the toggle switch is grayed out (inactive), then you need to log in to Windows using an administrator's account.) If the switch is not On, click it to turn it on. Setting your Internet connection to metered will prevent the download of updates to your computer without your express permission. That way you can wait until you are connected with unlimited data, such as cable or DSL, before you allow the update to be downloaded.
The look of Windows will begin to change with the Fall Creators Update. Microsoft is using a new language called Fluent Design to create the visual elements of Windows. Eventually, the look of Fluent Design will show up in apps. The first place you will see the changes show up is the Start menu if you have transparency effects turned on in the Colors settings. The Action Center also has a new design although its function remains the same.
The Photos app in Windows 10 will get a cool update that allows you to mix photos and videos and 3D effects into a video. The new features are based on a Microsoft project called Story Remix.
With Windows 10 Mixed Reality, you will be able to use virtual reality headsets that are cheaper and easier to use than those currently available. There are other improvements to the ability to play games coming with the Fall Creators Update.
The default Windows 10 browser Edge will now be able to work with PDF forms for filling out online information. You will be able to write notes directly on the page of a PDF if you have a touch screen. Reading e-books in Edge is also improved.
The new My People feature allows you to manage your contacts easier. You can pin individual contacts to the taskbar to optimize and streamline communications with those contacts without opening an app first.
There are also a number of security improvements, tweaks to accessibility features that allow users to type using eye-tracking technology (designed specifically for persons with ALS), improvements to the OneDrive cloud interface, more information about the status of updates, and the ability to insert emoji easily.
Microsoft has said it will release major feature updates to Windows 10 two times each year, spring and fall. Plan to take our Exploring Windows 10 course each fall to get up to date on all the changes from the previous year.
posted at: 11:01 | path: /windows | permanent link
Monday, September 18, 2017
Online Security Today
More and more, our everyday activities are conducted online, over the Internet. More and more, we hear horror stories of identity theft, cybercrime, companies with whom we do business hacked and personal information stolen, and individual's personal computer files held hostage to ransomware. Do you know how best to minimize the chance that you will be one of the unlucky ones who gets attacked by cybercriminals and hackers? Let's talk about the things you ought to do to protect yourself online, whether you are using a computer, a tablet, or a smartphone.
If you only use the Internet for entertainment and maybe a little Facebook or other social networking, you may think that you are not vulnerable. But you are. Every time you put some personal information on the web, you make yourself vulnerable to identity theft. A friend asks for your email address and you post it to her on Facebook. A relative wants your street address and you post it to him on Facebook. Now a hacker has two pieces of important information about you, enough for him (or her, but the fact is that most hackers are male) to take a closer look to see if you are worth the time to pursue. In any event, he may do nothing more than add you to a list of email addresses that he sells to spammers. So now you get more spam.
Hackers collect lots of information automatically by computer, save it into a database, and have the database mix and match the information to put names, street addresses, email addresses, social security numbers, etc. together for the same person. Over time, they accumulate enough information to access your banking and credit card information. It takes years of work to correct an identity theft. Protecting yourself is easier (but not necessarily easy).
Your first line of defense is to keep your operating system, whether Microsoft or Apple, up to date on your computer, tablet, or smartphone. These companies are constantly improving the security of the operating systems and you leave yourself more vulnerable than necessary by not staying up to date.
Use the latest version of a browser to access the Internet. The browser suppliers are also constantly improving the security provisions of their products. If your preferred browser is Window's Internet Explorer, you should be running version 11 (which also means you should be running Windows 7 or later).
Maintain up-to-date security software, such as anti-virus and anti-malware (malicious software) on your computer. The best of these are paid products, such as ESET, TrendMicro, Norton, BitDefender, and McAfee. There are some good free products available, such as Avast, Avira, and AVG. If you are on Windows, at a minimum, you should run Windows Defender. You should only install one anti-virus product on your machine; anti-virus software works so closely with the operating system that if two are installed, they may compete with each other and hang-up your computer, requiring you to re-start it.
Once you are online, your basic line of defense is your account password. Always use a different strong password for each important account. The strength of a password is based mostly on its length, how many characters it has. Your passwords should have at least 12 characters. Length is more important than symbols and punctuation in the password (although many accounts require them). That is, a password like "HOUSE BLUE DINNER WATER" is more secure than "jU?&_2n." (Note: most of the strength meters available on the Internet do not give accurate results.)
So how do you remember all those long, strong passwords? Two ways: keep a dedicated notebook (that is stored securely, away from your computer, when you are not using it) or use a software password manager such as LastPass, 1Password, KeePass, or clipperz (you can search for those on Google or other search engine to learn about them).
Always use two-step authentication if it is available. This authentication adds a second step to logging in to an account. After you enter your password, the authentication process sends a code to your cellphone or to an email account that you own. You have to submit the code to the account to successfully access it. Since the code is being sent to a physical device or email account that you control, someone trying to break into your account will not have access to it. This is not as inconvenient as it sounds as you can register your computer, tablet, or smartphone with the account so it doesn't ask for the second code if you are accessing the account from that device. The intent is to keep others out of your account.
Once you are online, be wary of any link or popup that is not familiar. Be especially wary of any link sent to you on Facebook, Twitter, Instagram, or other social networking site. If you have decided that a site is safe and it asks you to submit personal information, make sure the URL (the Internet address in the address bar of the browser) begins with https://, not just http://. The "s" in the former indicates that information sent to the site will be encrypted, making it much harder to use even if it should be intercepted by a hacker.
posted at: 12:36 | path: /www | permanent link
Thursday, September 14, 2017
Wikipedia
I was born in the 1940s, long before the Internet came into being to supply information. For someone like me, who loved to read and wanted information about everything, there was a means. Door-to-door salesmen walked the neighborhoods, selling encyclopedias: Britannica, Compton's, World Book, Funk & Wagnalls. I was lucky enough that my parents wanted me to have access to information and bought a set of Compton's, which I assume was the cheapest since my parents were cotton-mill workers. Oh, the wonderful hours I spent poring over every volume in that set. I still like to learn about new things. Today I use the World Wide Web over the Internet. Specifically, I use the web site Wikipedia.
Wikipedia is an online encyclopedia. You can find it at http://wikipedia.org. There are two amazing things about Wikipedia. First, it is free. Second, it is written by us, the public. Anyone can contribute an article on any subject or edit information that is already published on the web site.
You would think that this would lead to volumes of inaccurate or intentionally misleading information, but it doesn't, at least not for mainstream topics such as medicine, history, arts, computers, technology, and others. Here's why: Wikipedia, like other wiki sites on the web (there are many) is based on software named wiki by its author. That software allows one to edit a wiki site web page directly through a web browser (any browser, such as Chrome, Firefox, Safari, or Internet Explorer). For every active wiki site on the Internet, there develops a community of users that contribute and edit the information. They take pride in accuracy and completeness. Many strive for a "neutral point of view," Wikipedia's guiding principle. The community won't let inaccurate and misleading information added by a user remain posted for long. In research to write this article, I came across a challenge to anyone who doubts this. The author suggested that you add intentionally inaccurate information to any mainstream Wikipedia topic and monitor your posting. He predicted that within 10 minutes a Wikipedia community member would correct it.
You may wonder what this wiki software is. Wiki was invented by Ward Cunningham in 1995. The word "wiki" is Hawaiian for quick and Cunningham was looking for a word to call his software that conveyed how quickly web pages could be created and edited with it. He published the first wiki web site, for computer programmers to collaborate, at http://wiki.c2.com. It's still there, although active editing stopped in 2015. Editing directly on the web is exactly the collaboration that Tim Berners-Lee envisioned when he invented the World Wide Web in 1991. Berners-Lee's first simple browser included editing capability. He did not have the time, however, to produce a full-featured browser. When Marc Andreessen wrote the first one, Mosaic (later Netscape), he focused on publishing, not collaboration.
Wikipedia is the largest wiki ever. The English language version has over five million articles, on virtually any topic you could want information about. Over 1,200 volunteer administrators keep watch over Wikipedia. On December 2, 2016, the Wikipedia site showed about 125,000 "active users," defined as users who had made an edit to a article in the past 30 days.
Several studies of the accuracy of Wikipedia's entries have been made. For mainstream topics such as medicine and technology, those studies have found Wikipedia to be as accurate as other encyclopedias. Even schools and universities are beginning to accept Wikipedia as accurate enough to cite. In any event, every Wikipedia page has citations at the bottom so you can double-check the information if you need to. All in all, Wikipedia is a good starting point to learn about any topic.
posted at: 12:02 | path: /general | permanent link
Tuesday, September 12, 2017
Macbook Pro
After almost 30 years using Windows PCs exclusively, I recently bought a MacBook Pro. Why? Well, it all started with an iPad. The organization where I volunteer to help others use computers was strictly Windows PCs until 2013. Then we started teaching iPad and iPhone courses. So I mentioned to my wife that I was thinking about getting an iPad to help out with those courses. And she got me one for my birthday.
At that time, I used a Motorola Droid4 Android cell phone. It never seemed smooth and responsive to me and its battery life was terrible. I played around with my wife's iPhone and liked it. So when the Droid died, I decided to try an iPhone. Loved it.
What amazed me was how easily and automatically the iPhone and iPad communicated and kept everything synced and up to date.
Then we started to teach Mac computers. That got me thinking. If the iPad and iPhone synced my calendar and reminders so easily, could a Mac computer do that also? I talked with a few friends that had Macs and they thought it could. I've always thought Apple products were better built than PCs. The screens, especially the Retina models, were certainly prettier to my eyes. So I took the plunge and bought the MacBook Pro. It's been fun learning the new systems and apps. One of these days, maybe I won't have to work so hard to remember if I'm sitting at a Windows machine or a Mac when I try to do something.
posted at: 11:12 | path: /mac | permanent link
Thursday, August 24, 2017
Who Invented the Internet
The Internet pervades our lives. There is almost no one whose life is not touched by it. For many of us, the Internet seems like a necessity. We do our banking using it. We get our news from it. We keep up with family and friends over it. We use it for our entertainment. How did it come to be? Who invented the Internet? (Hint: It was not Al Gore, although he did play an important role as a government leader in supporting its creation.)
The answer is that no one person invented the Internet. It was a collaborative creation that evolved over twenty years, from 1962 until 1983. During that time, a number of different technologies were invented by different men. These technologies were the building blocks of the Internet and until each was fully working, they could not be combined to make the Internet we use today.
Even before the specific technologies were developed, there had to be a visionary. In this case, it was J.C.R. Licklider, a psychologist who worked on human-computer interfacing for years. Licklider was inspired in his vision of managing computer information by Vannevar Bush, head of the U.S. Office of Scientific Research and Development during World War II. In July 1945, Bush published an essay in The Atlantic magazine entitled As We May Think. He set forth a vision of how information could be made readily available at a desk, with a means to link different parts of it. Bush was also instrumental in creating the National Science Foundation (NSF), which later played a key role in creating the Internet.
The spark that lit the fire behind America's development of the Internet came from across the seas. In 1957, Russia launched Sputnik. In response, the Eisenhower administration established the Advanced Research Projects Agency (ARPA) under the Department of Defense.
ARPA led the initial efforts to get America into space and to ensure that America remained at the forefront of innovative technology. ARPA worked by funding research at companies such as Bolt Beranek and Newman (BBN) and universities such as MIT and Stanford. After the space efforts were transferred to NASA, ARPA turned part of its efforts to information technology. It established the Information Processing Techniques Office (IPTO).
In 1962, J.C.R. Licklider became director of IPTO. Licklider had for years advocated sharing computers over a network to solve technical and communication problems. He playfully called it the Intergalactic Computer Network. He convinced Ivan Sutherland, Bob Taylor, and Larry Roberts of the usefulness of networked computers. Each of these men headed IPTO after Licklider and carried his vision forward.
Licklider could not develop the network of his vision because the technology was not sufficiently advanced during his tenure at IPTO. By 1966, Bob Taylor decided that it was time. There were other networking efforts going on in the world using different technologies. In fact, the proliferation of incompatible systems was a reason to move forward. Taylor brought in Larry Roberts to head up the effort to build the network, eventually called the ARPANET.
It took three years before the ARPANET connected computers at UCLA and Stanford Research Institute. In October 1969, the first transmission (of the word login) between two networked computers took place. Leonard Kleinrock of UCLA was one of the team present when that first message was sent. He told in an interview how the system crashed when the letter G of login was typed and said, "Yet a revolution had begun."
In a matter of months, network connections were made to the University of California Santa Barbara and the University of Utah. ARPANET, the first computer network, was a reality. Growth was rapid after that, but limited to government, research companies, and universities, because they were the ones with computers, all of which were big, expensive mainframe computers. The widely available, personal computers of today were not invented until 1977.
So did the ARPANET become the Internet? Not exactly. The ARPANET was a single network, even after it expanded to hundreds of computers. The Internet is a network of networks. The key technology of the Internet -- the protocol controlling the connections among computers -- was developed by ARPA. In 1972, Larry Roberts wanted to connect satellite communications to the ARPANET. He gave the job to Bob Kahn, who brought in Vinton Cerf of Stanford University to help him develop the connection technology. It took two years for them to develop and refine the Transmission Control Protocol/Internet Protocol or TCP/IP and another eight years to convince the Department of Defense that it was reliable enough to use. On January 1, 1983, the ARPANET was switched to TCP/IP. This date can be viewed as the birth of the Internet. Cerf has often been called "the father of the Internet."
TCP/IP was public information, developed with taxpayers' money. Others began to use it even before the ARPANET did. The most important of these was the National Science Foundation's NSFNet, launched in 1986. Its goal was to connect every academic researcher in the nation. With government funding, the NSFNet network backbone replaced the ARPANET as the basic network underlying the Internet. The ARPANET was formally shut down in 1989.
By 1991, researchers were sending emails and using the Internet for accessing information using tools such as Archie and Gopher. But it was not easy to find that information and the use of the Internet was small scale compared to what was to come. For in that year, Tim Berners-Lee invented the World Wide Web or WWW and Al Gore sponsored bills to allow commercial enterprises to connect to the Internet. The commercial networks, mainly from the telecommunication companies, became the Internet. Its use exploded because the WWW and web browsers made it easy both to put information on the Internet and to find it. Surfing the Internet became a part of almost everyone's life.
posted at: 12:43 | path: /www | permanent link
Saturday, May 13, 2017
Apple versus Microsoft--a Little History
In 1981, when Microsoft provided the operating system for the original IBM Personal Computer (PC), it retained the right to sell that operating system to other computer manufacturers. Thus was born the PC clone market. Many manufacturers entered the market and by the mid-1980s, inexpensive PC clones dominated the hardware side of the market. Microsoft dominated the software side. That basic fact -- that Microsoft is a software company and Apple is a hardware company -- accounts for the basic differences between PCs and Macs.
Apple co-founder Steve Jobs said, "Apple strives for the integrated model so that the user isn't forced to be the systems integrator." This meant Apple designed its computers from the ground up to adhere to certain standards and to operate the computer a certain way. As a result, Apple hardware is better built and more attractive than PC hardware, but is generally more expensive.
Because it provided its own software (both the MacOS operating system and basic applications), tailored to its hardware, Apple could provide a more stable system. PCs running Windows had to live in the world of device drivers to provide the interface between the Windows operating system and the myriad of different hardware configurations that the PC manufacturers produced. As a result, Macs do not crash as frequently as Windows PCs. Also as a result, however, PCs evolve more rapidly because of the competition among all those hardware manufacturers. A prime example is gaming. Windows PCs dominate the gaming market because of quick development and deployment of improved video adapters.
Because Steve Jobs believed he knew what users needed, Apple computers usually give you one way to perform a given action. Windows, on the other hand, gives you multiple ways. A Windows PC is highly customizable, a Mac not so much. Customization is a two-edged sword. As a result of all the options, Windows is more difficult to learn than macOS. However, if the Mac's way does not seem intuitive to you -- although Apple does a good job of making most basic actions intuitive -- you have fewer options to change it.
posted at: 10:45 | path: /general | permanent link
Friday, December 02, 2016
Ad Blockers
I formerly used a hosts file to block domains from which ads are served. (If you want to know how to do this, go to this page.) In the past few weeks I've seen a new response from some web sites that pop-up a window that asks to be white-listed or to pay a fee to continue to read. Guess the site owners are tired of not getting their ad revenue. Can't blame them.
posted at: 09:14 | path: /www | permanent link
Sunday, May 10, 2015
Lake Jocassee Tour
Debbie and I toured Lake Jocassee with Lake Jocassee Tours. Brooks and Kay do a great job. This tour featured the full moon rising. We spent about 3 hours on the water, meandering in and out of coves along the eastern shore to see waterfalls, flowers, and foliage. You can see some of the pictures we took.
posted at: 18:22 | path: /travel | permanent link
Tuesday, September 23, 2014
Is There Really Such a Thing as Plain Text?
This article says no, plain text is a lie. I don't see it that way. The article is really talking about making sure you have your encoding correct and it does a great job of explaining why. To me, however, plain text in English is ASCII. It's been around for over 50 years. It will render correctly in all cases. I recognize that the Internet has made it necessary to provide for other languages and that is where Unicode comes in. For that, you definitely have to make sure you announce your encoding, as the article says. The article also recommends that you read Spolsky's article about encoding. I second that recommendation.
posted at: 11:36 | path: /plain_text | permanent link
Sunday, February 09, 2014
Batch Files
Batch files are command-line scripts for Windows. They can be used to automate tasks on your computer. Batch files or scripts can be used for backup, moving to a project-related directory, cleaning up your hard drive, and almost any other task you can do from within Windows.
The Windows batch scripting "language" is not as fully capable as *nix shell scripting. Microsoft has provided a new tool, PowerShell, to improve Windows scripting capability. PowerShell gets good reviews, but it is a completely new language that I haven't gotten into yet, so you will not see much about it here.
Batch files, with the file extension .bat, have been around since DOS. The commands available for scripting have increased significantly since Windows NT and scripts that take advantage of those additional commands may have a file extension of either .bat or .cmd, the latter indicating that NT and later commands have been used and the script likely will not run under DOS or Windows 9x. I'll be writing more about specific batch scripts that I use, but here is an article on batch file basics that is more complete than I would ever provide. I have not read the book from which the article is taken, but it gets good reviews and the same author has written an update entitled Windows 7 and Vista Guide to Scripting, Automation, and Command Line Tools that covers Windows 7 and PowerShell. But the linked article will get you started on the basics of batch files.
posted at: 15:00 | path: /windows | permanent link
Tuesday, January 21, 2014
Windows Command Line
I used to use the command line in Windows a lot. Almost all of my backup and other disk cleanup activities were done through batch files (command line scripts), which are just automated typing of command line commands. For someone like me who likes to use text files for all the important stuff, learning to use the command line in Windows was the key to productivity. Best tutorial I've found for this is Zed Shaw's Command Line Crash Course. Go read it.
posted at: 09:34 | path: /windows | permanent link
Thursday, May 23, 2013
130 Pages??!!
I had a page about Markdown. It was about 15 or 20 screens of information with a comfortable layout with lots of whitespace. I thought it was a relatively complete description of Markdown. Now I find a McSparky book on Markdown that has 130 pages and 27 screencasts to discuss Markdown and how to use it. How do you write that much about a tool as simple and straight forward as Markdown? I don't know yet and haven't decided if I'll spend the $10 to find out. But it comes highly recommended. My curiosity may get the best of me. UPDATE 2019-04-29: After I bought my Macbook, I decided to buy the book. Most of it is about tools that you use Markdown with rather than Markdown itself. It's a good book, but the Markdown part is not worth the money; the other parts may be if you need that information.
posted at: 08:44 | path: /plain_text | permanent link
Friday, February 01, 2013
Tools Reviews at ProfHacker
One of the writers at ProfHacker put together a summary of their reviews and comments about tools they use. Here is the lead:
Here's a collection of posts from the archives that focus on the use of plain text editors and alternative word processors.
Good stuff.
posted at: 07:18 | path: /plain_text | permanent link
Friday, January 11, 2013
Markdown
Markdown is a Perl script to convert a readable plain text document to valid HTML content for the web. The plain text document is marked up with simple markup to produce headings, emphasis, links, etc. I wrote a tutorial for Markdown mainly to learn about it. By writing a tutorial in Markdown itself, I could quickly learn all the features of the markup. Using a tool fixes it more securely in your mind than just reading the syntax--at least it does in mine.
posted at: 07:46 | path: /plain_text | permanent link
Thursday, January 10, 2013
What I Know About Using Plain Text
The benefits of using plain text for all the information you want to retain are simplicity, portability, and durability. Almost every application has the capability to import and use plain text. The recent example of Microsoft Word files is a good one to illustrate the barriers created by proprietary file formats. For the 2007 version of Word, Microsoft changed the format of the created documents to one based on XML. The change is an improvement, but older versions of Word cannot open the new format without additional software. In other words, the new format is not forward compatible. Because this is a recent change, the additional software to work around the incompatibilities is readily available. But consider the situation 10 years from now. As this article from Macworld magazine says, sometimes you can't even open your older documents. You never have to worry about that situation with plain text. Or the situation of changing to different software. As noted, almost all software can import plain text so it has ultimate portability.
If that's the case, why doesn't all software simply operate in plain text? Because it's "plain." No formatting, no bold, no italics, no spacing control other than a blank line and spaces or tabs. The plain in plain text results from the fact that the foundation of it is ASCII encoding that included only the upper and lower case English alphabet, numbers 0 - 9, basic punctuation, and a few control characters. Encoding is a code relating the alphanumeric characters to numbers ('cause computers don't speak English). Encoding in ASCII is a basic foundation of plain text. For a full definition, read the Linux Information Project's Plain Text Definition.
The ASCII encoding is one of the earliest, having been established in 1963. Because ASCII is limited to the English alphabet, more recent encodings have been established to encompass more languages. The current trend is toward Unicode encoding, which has the ambitious goal of encoding every character in every language in the world. Unfortunately, there are several versions of Unicode (e.g., UTF-8, UTF-16) as well as other encodings (e.g., ISO-8559, Windows 1252, and many more). Fortunately, the most frequently used ones are a superset of ASCII. In other words, even the most modern encodings, now fifty years from when ASCII was established, can still display ASCII files correctly. Thus, from a durability point of view, it's a good bet that files created in plain text today will be accessible over a lifetime at least.
That does not mean that there might not be some issues. Almost all of us have seen occasions when a web page displays a few characters that do not make any sense. For example, quotation marks may appear as gibberish or a question mark rather than an actual quotation mark. This is almost always the result of the browser using a certain encoding to display the page when the text is actually encoded using a different encoding. Web pages are supposed to inform the browser what encoding is used. Many, however, don't and the browser has to guess. If it guesses wrong, the user suffers by having to figure out what those gibberish characters are.
The bottom line is that if you predominately use the English alphabet for your documents, keeping to plain text will ensure that you can access and use them in the future.
posted at: 17:16 | path: /plain_text | permanent link
Thursday, January 03, 2013
Using Plain Text
UPDATE 2019-05-11. Some of the links in this post are dead. It you have an interest, you may be able to find the articles at web.archive.org.
I have always been fascinated by what tech experts could accomplish with plain text. They could keep notes and articles in plain text for simplicity, portability, and future retrievability, then turn those files into formatted, structured documents through the magic of markup or filters. Years ago, I began to keep my personal notes and information in plain text because files were small and search was fast. I never, however, really learned how to manipulate text. I came out of the corporate environment, a lifelong Windows and Office user. I didn't have the exposure to Unix and the Unix tools to manipulate text. I didn't know how to do the magic I saw others doing. I'm now retired, so I decided to learn more about the foundation of using text.
How I Started with Plain Text: I don't know when I first read Merlin Mann's 43Folders, but I do recall that his post about using plain text was one of the first I read on the subject. Really savvy tech experts, called "alpha geeks" by Danny O'Brien, frequently prefer plain text to get their work done. O'Brien surveyed his tech friends and publicized this preference for simple approaches in 2004. The information from those links got me interested. The links below gave me a feel for what others were doing with plain text.
- more on O'Brien's life hacks
- using one big text file for everything
- living in text files
- more from 43folders
From there I began to explore the tools I could use for plain text information storage and retrieval. Little did I know that the exploration would continue until now. I'm still working to master using text.
posted at: 09:03 | path: /plain_text | permanent link
Monday, February 13, 2012
Definition of Capitalism
An amazing story from China.
posted at: 09:41 | path: /general | permanent link
Thursday, December 08, 2011
Can Anyone Create Jobs?
One of the most coherent, logical newspaper articles I've read in some time. Recommended reading.
posted at: 14:41 | path: /general | permanent link
Friday, July 22, 2011
It's Really Pretty Simple
The title is talking about defining the problem, not the solution, to our national debt. The solution is tied up with political maneuvering by the same politicians that have ignored the clearly-approaching problem for 30 years. This article summarizes it well. For the past 60 years, the government has averaged receipts of 18 to 19 percent of GDP. Therefore, we cannot average more than that in spending or we add to the already unacceptably large deficit. In 2010, we spent 25% of GDP. Continue that and the defaults that are being talked about as possibilities come next Wednesday become the norm and the U.S. is on its way to becoming a second-rate nation.
posted at: 11:23 | path: /general | permanent link
Saturday, June 11, 2011
Quotable Card
I like Orson Scott Card's books and his web site. He also says things that I consider eminently quotable, such as:
"… you can't go broke underestimating the taste of the American people."
--Orson Scott Card, here
and
"After all, we rarely understand our own motivations, and so, even when we write down what we honestly believe to be our reasons for making the choices we make, our explanation is likely to be wrong or partly wrong or at least incomplete."
--Orson Scott Card, Shadow of the Hegemon
posted at: 09:17 | path: /reading | permanent link
Friday, June 03, 2011
Models
I spent almost 30 years in environmental affairs and remediation work for a corporation. Many times I railed at the money industry had to spend based on a model that some agency or consultant had constructed, many times without needed data and with questionable assumptions and inputs. Now, in retirement, I'm worried about this country's future given the fiscal mess we're in. So I was transported back in time when I read this article about models used to assess the impact of cuts in spending or increases in taxes. Deja vu all over again. I have no idea if the author of this article knows what she's talking about. But there's enough questions in there to make you wonder if anyone really understands what we can do and what the consequences will be when we do it. Go read it.
posted at: 14:38 | path: /general | permanent link
Saturday, May 28, 2011
What is Valid?
When I think of all the resources that have been squandered based on "new scientific findings" it makes my stomach ache. Don't get me wrong, science and technology have been the very foundation of this wonderful life that we now enjoy. But when you study something as complex as human health or the environment, you can gather such a small part of the data that influences the systems, it is easy, too easy, to draw the wrong conclusion. Then we're spending resources on the wrong thing. This post from Stephen Bainbridge talks about a recent "correction" of past conclusions. Here is his concluding paragraph:
"The point is not that we should ignore environmental concerns. The point is that we should be wary about claims that massive social and economic changes are necessary simply because the scientific consensus of the moment claims they're desirable. Like the medical claims about salt I mentioned in my earlier post, and like this latest news, the consensus of the moment can turn out to be seriously flawed."
posted at: 07:16 | path: /general | permanent link
Monday, April 11, 2011
The Problem with Social Security
Other than the fact that it was originally passed to be an emergency measure to keep people from starving and has had significant payment and tax increases over the years, the basic problem is life expectancy. In 1935 when Social Security was passed, the average life expectancy at birth of males (who constituted most of the workforce at that time) was 60 years. In other words, the Congressmen who passed it did not expect most workers to live to collect a dime since the qualification age was 65 years. Now life expectancy at birth is about 78 years. So we went from few collecting benefits to almost all of us receiving benefits for 13 years on average and at increased payouts. No wonder it's sopping up more and more of our country's revenue every year! Time for a change!
posted at: 18:17 | path: /general | permanent link
Wednesday, January 26, 2011
Can the U.S. Survive?
Robert saw it long ago:
"The America of my time line is a laboratory example of what can happen to democracies, what has eventually happened to all perfect democracies throughout all histories. A perfect democracy, a 'warm body' democracy in which every adult may vote and all votes count equally, has no internal feedback for self-correction. It depends solely on the wisdom and self-restraint of citizen...which is opposed by the folly and lack of self-restraint of other citizens. What is supposed to happen in a democracy is that each sovereign citizen will always vote in the public interest for the safety and welfare of all. But what does happen is that he votes his own self-interest as he sees it...which for the majority translates as 'Bread and Circuses.'
'Bread and Circuses' is the cancer of democracy, the fatal disease for which there is no cure. Democracy often works beautifully at first. But once a state extends the franchise to every warm body, be he producer or parasite, that day marks the beginning of the end of the state. For when the plebes discover that they can vote themselves bread and circuses without limit and that the productive members of the body politic cannot stop them, they will do so, until the state bleeds to death, or in its weakened condition the state succumbs to an invader -- the barbarians enter Rome."
--Robert A. Heinlein
posted at: 12:44 | path: /general | permanent link
Tuesday, December 14, 2010
A Simple Life
The key to living a simple life is consistency. The key to consistency is self-discipline. But why is it so hard?
posted at: 13:10 | path: /general | permanent link
Friday, November 26, 2010
Making a Presentation
I spent 40 years in a corporate environment. Early on I realized that making an effective presentation to a group was key to my ability to do a good job. By communicating clearly, I could provide co-workers with the information they needed to do a good job, especially on my projects, and managers with recommendations they needed to support their job, and perhaps my advancement. So I worked hard at it.
In the late 1960s, when I began my career, using transparencies with overhead projectors was the way to illustrate your points. At first, you used the transparency interactively -- you wrote on it during the presentation with a wax pencil. This "evolved" to preparing bullet lists before the presentation that would be shown on the screen. Then, in the mid-1980s, PCs came in and the production of bullet lists became "beautified." You made your lists in a word processor and printed the transparencies, all in black and white. As PCs progressed, clip art, color, different fonts, different viewpoints became possible and the transparencies got fancier and fancier. Then the overhead projectors were replaced by computer-driven projectors and computer applications to make the slides took over, allowing you to produce animated slides with color, thousands of fonts, and even sound. So the presentations began to be the focus and they got even fancier and fancier. It took a while to realize that they were also getting muddier and muddier, with the message being further subordinated to the exoticness of the presentation.
Today, and for the last 20 years, PowerPoint is the ruler of the slide-making software. You can now download complex templates to help you make any point you want in as fancy and complex manner as you want. The question is, should you want?
I came to understand late in my career that PowerPoint hurts more than it helps in making an effective presentation that your audience will remember. No less an authority than Edward Tufte makes a damning case against the way PowerPoint is usually used. But it does not have to be used this way. PowerPoint can be effective if you follow a few rules.
- People remember what you say, not what you put on the slide. Say it clearly and enthusiastically.
- A slide should have no more information on it than your audience can comprehend in less than 5 seconds.
- Use your slides for concise bullet points or simple data graphs that illustrate what you are talking about.
- Use animations sparingly. An effective use of PowerPoint animinations is to highlight the point you are currently talking about while you dim the other points.
posted at: 20:55 | path: /general | permanent link